"The government's been in bed with the entire telecommunications industry since the forties. They've infected everything. They get into your bank statements, computer files, email, listen to your phone calls... every wire, every airwave. The more technology used, the easier it is for them to keep tabs on you. It's a brave new world out there. At least it better be."
--Brill (Enemy of the State)
A growing theme of political discourse involves complaints about violations of what is commonly called 'right to privacy.' Concerns are being voiced about spying, surveillance, hacking into the private affairs of others. On the back of last week's accusation by President Donald Trump that his predecessor was tapping his telephones during the 2016 presidential campaign, Judge Nap explains how we have arrived at this point.
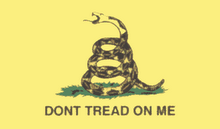
A key driver of the American Revolution was liberal use of general warrants by the British. At their discretion, British soldiers could write up an order that authorized them to search the property of any colonist. After the revolution was won, the framers wrote the Fourth Amendment to expressly prohibit the use of general warrants.
The Fourth Amendment clearly states several requirements for valid warrants. Warrants must be specific as to the person and place to be searched. Warrants must be accompanied by evidence of 'probable cause' to justify the search. Warrants must be issued by a judge who weighs the evidence and decides whether the probable cause evidence justifies a warranted search.
A major blow to right to privacy occurred in 1978 with the implementation of the Foreign Intelligence Surveillance Act. The act, introduced by Senator Ted Kennedy and signed into law by President Jimmy Carter, placed a secret judiciary (now known as a 'FISA court') between the nation's spies (e.g., the NSA) and foreign agents. The original theory was that the NSA would have to demonstrate to the secret FISA court probable cause that individuals to be spied upon were agents of foreign powers. By employing the FISA court as intermediary, it was thought that the NSA would be restrained from spying on ordinary Americans.
But even in its original form and intent, the FISA act constituted a dramatic federal government rejection of the constitutional standard that probable cause of crime must be apparent for the issuance of a warrant. Simply put, foreign agency, by itself, is not a crime.
Thus began the trip down a slippery slope that was all too predictable. Probable cause of foreign person hood morphed to probable cause of talking to a foreign person which morphed to probable cause of being able to talk to a foreign person which morphed to dropping the probable cause standard altogether.
The twisted logic became anyone who speaks to anyone else who could ultimately speak to a foreign person should be subject to surveillance. By extension, the NSA argued that it would be more efficient to spy on everyone in the United States than to isolate people deemed as 'bad.' The courts bought that argument.
As such, FISA warrants have become consummate general warrants. They allow intelligence agents to listen to whomever they wish and to retain whatever they hear.
Subsequent extensions of Owellian FISA laws, such as the Patriot Act and other programs done in the name of national security, have multiplied the number of jackboot prints on the Fourth Amendment.
The digital nature of modern communications permits the NSA to capture all keystrokes made on networked computers in or linked to the US. NSA also captures all phone conversations made within the US or to someone in the US. The NSA can download any phone conversation, text, or email at will. The NSA captures the digital equivalent of 27 Libraries of Congress each year.
Let's return to accusations that Obama was behind a FISA warrant to obtain Trump phone conversations during the presidential campaign. The accusations are absurd because he doesn't need a warrant. The NSA already has digital copies of all Trump phone conversations for the last 10+ years. Because the NSA is part of the Department of Defense, it is subject to the orders of the president in his capacity as commander in chief.
If the commander in chief wants something that a military custodian already has or can create, such as transcripts of an opponent's phone conversations with political strategists during a presidential campaign, he merely has to ask for them.
After fighting wars to preserve our right to privacy, we have allowed our elected representatives to crush that right.
Thursday, March 9, 2017
Spies Like US
Labels:
agency problem,
Constitution,
founders,
judicial,
liberty,
natural law,
property,
security,
war
Subscribe to:
Post Comments (Atom)
![[Most Recent Quotes from www.kitco.com]](http://www.kitconet.com/charts/metals/gold/t24_au_en_usoz_2.gif)


No comments:
Post a Comment